Get your images SEO'd and Ready to Go with all your apps and sites. We'll work together with the latest Best Practices and AI tech to optimize the images you have and create new ones to solidify your SERP Ranking. Get Optimized and Accessible Publish Search Engine Optimized images to all of your apps, sites and product…
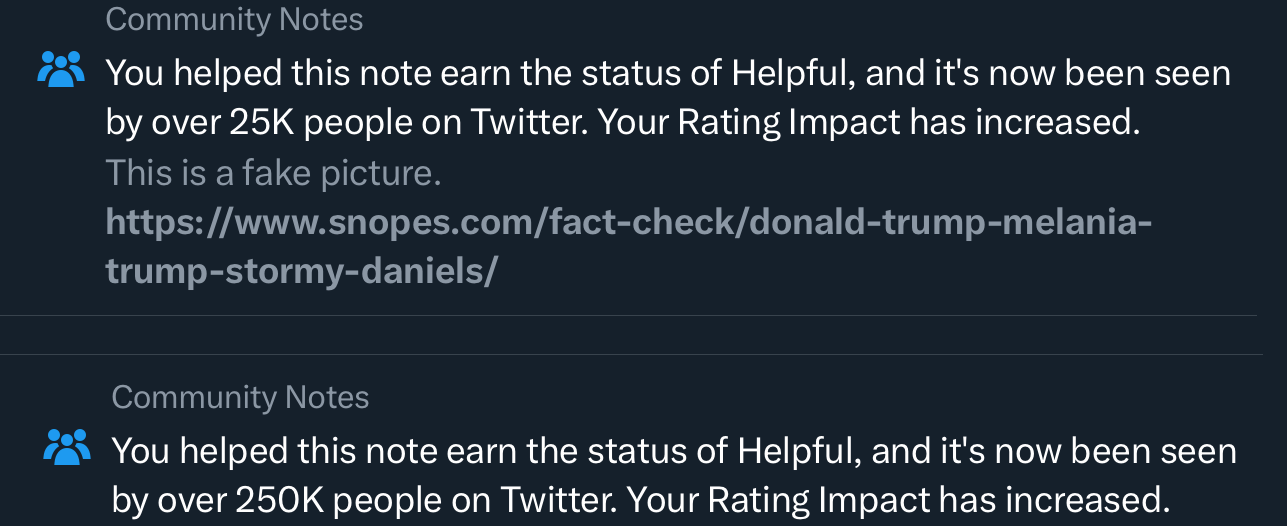
“Community Notes” by twtr
Community moderation, paid editors, and the latest AI and machine learning tools assisting all involved are core to addressing misinformation and disinformation at global scale.
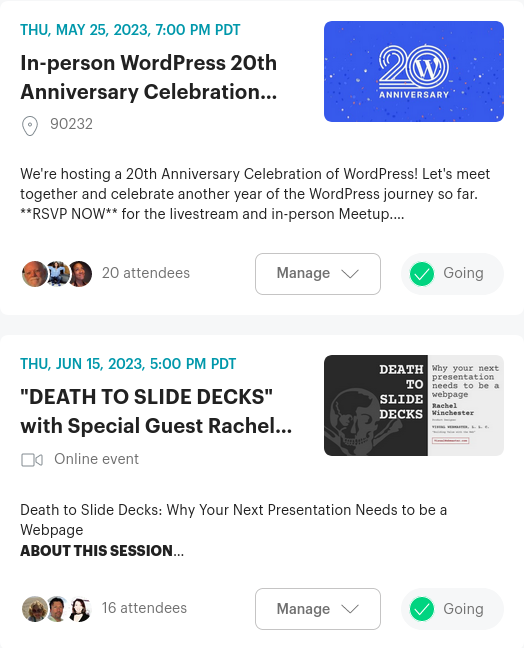
Organizing Meetups on Meetup.com
Organizing Meetups on Meetup.com will be much smoother once I learn how to Preview things and call-out individual people. Previewing pre-publish is essential. Meetup does a good job with Event draft previews. The same type of preview for Discussions and Comments would be a boon. This previews what my [content] will look like before going…
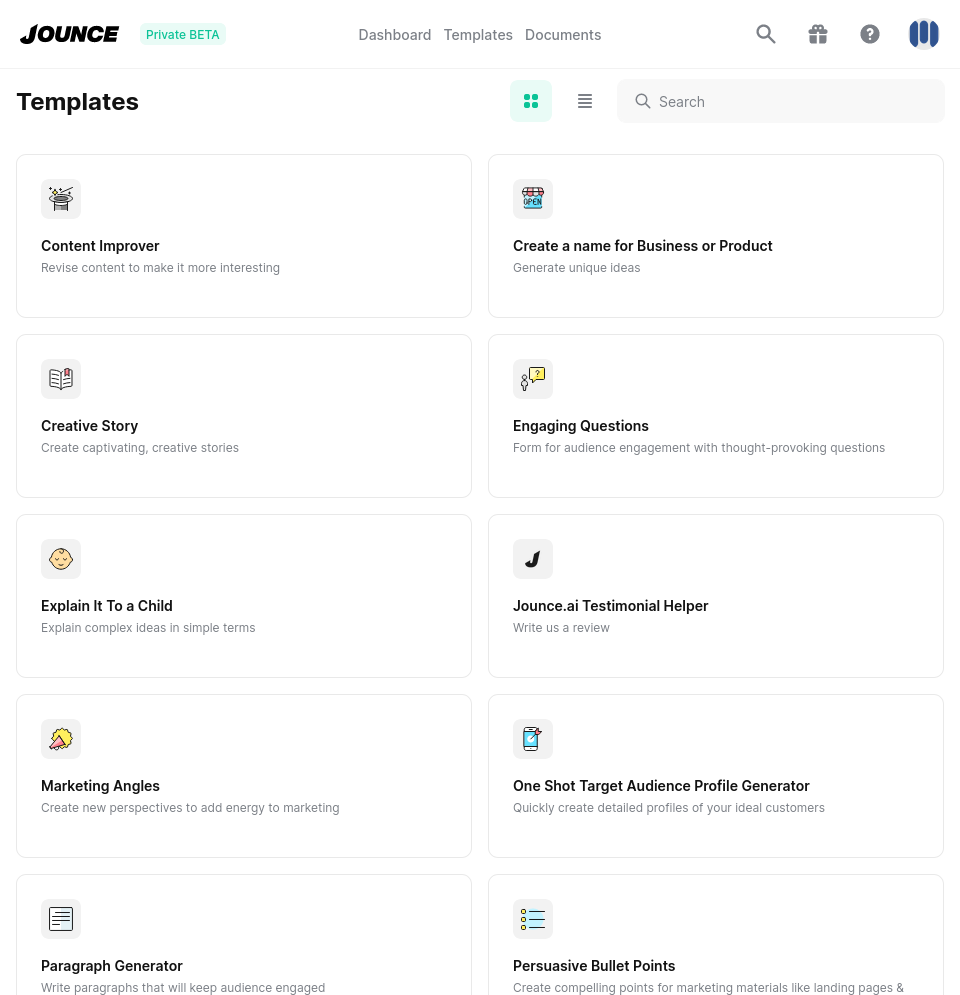
Jounce through the Paces
Applying what Jounce does to Work-in-Progress -- real notes, code, and copy -- are opportunities to review and tweak prompts, chains, results and discover more possibilities.
Jouncing the Limb
Jounce delivers solid baseline results which get better as refine my prompts and familiarity with the tool. Jounce's dozens of templates are good for guiding your prompts, and results are saved in your "History" of each template by default. The structure of each template is clear -- How my input is being used and where…
Suggestions, Recommendations
Suggestions are made with context from content, authors, activity streams, and social signals. Presenting people with suggestions at the right time are opportunities to recommend a change to make or ignore and surfaces other ways to tailor their experience. https://meanbusiness.com/2021/11/02/the-tools-we-use-app-context/
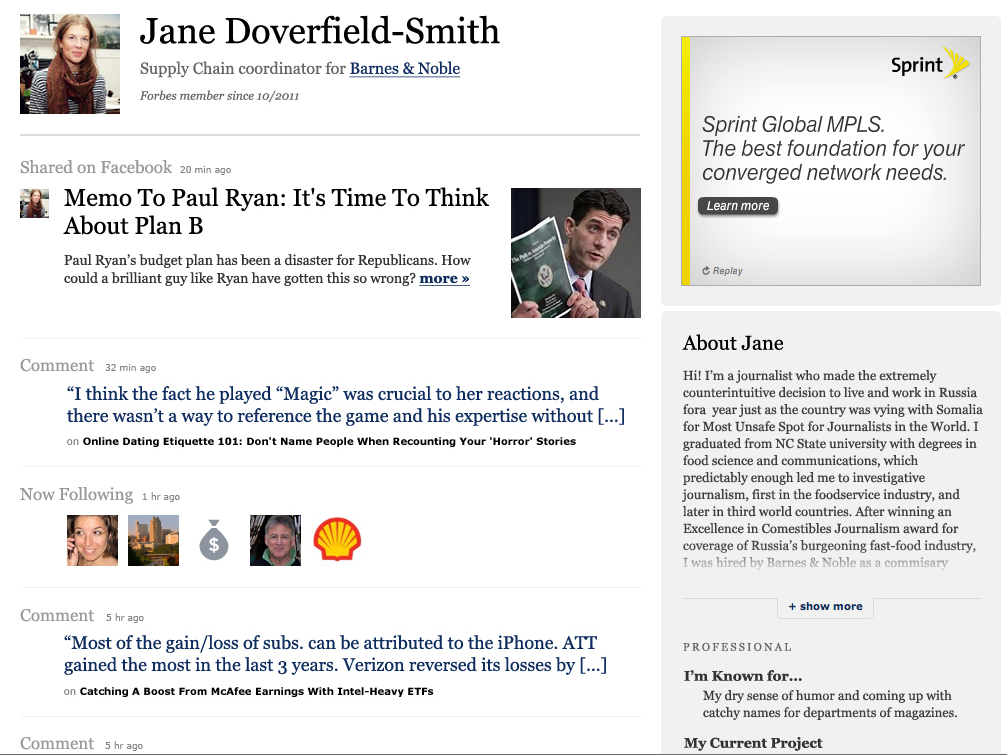
Member Profiles: Core+
Contact info and preferences, social channels, activity streams, account management
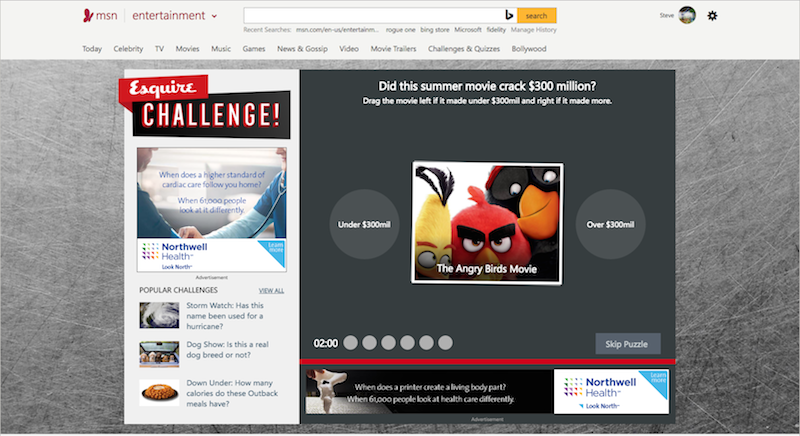
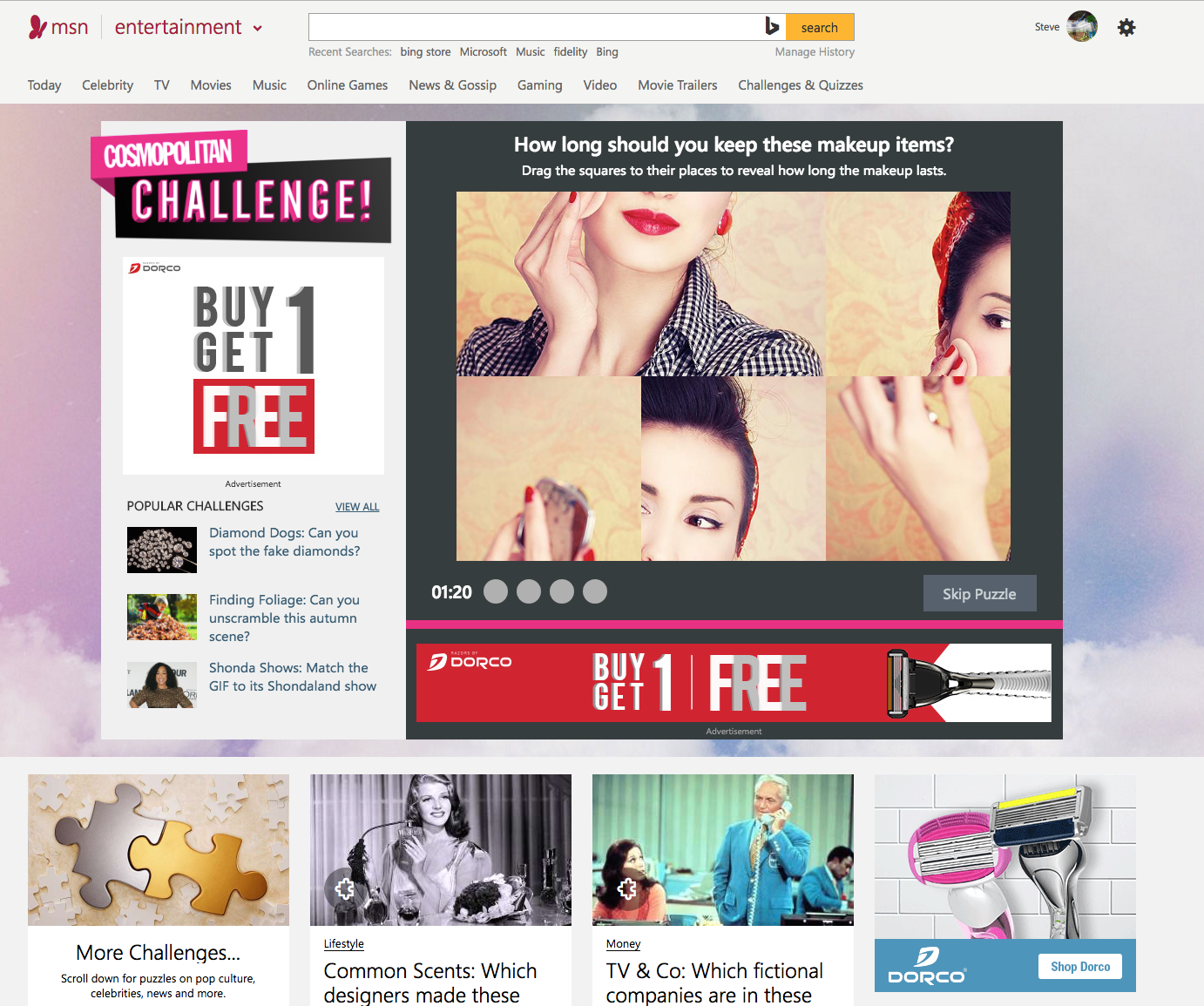
Game Teams @ Hearst
Millions of people playing games every week gave all teams involved clear insights to act on live and in-flight and for the next product iterations.
Product Revenue & Sales Funnels @ Hearst
Engagement from readers, viewers, and players informed opportunities across Hearst brands and businesses
Products for Editors @ Hearst
Products that work the way Editors do. Smart tools and workflows that get smarter.
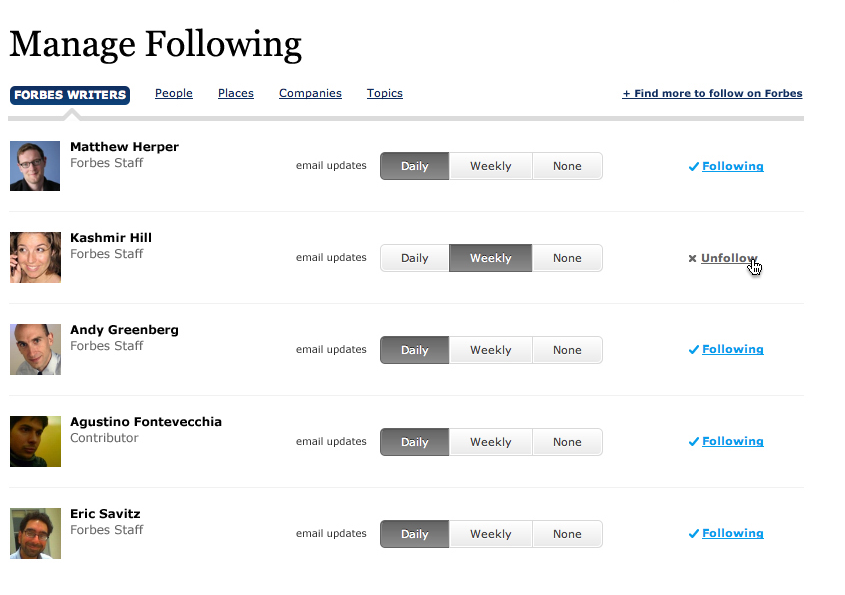
Forbes “Following”
Content Tools @ True/Slant
Editors at True/Slant made updates to stories, topics, and promotions directly from the live site. Edit options appeared only for people with access to them. Edits made were contextual to the page, topic activity stream, or promo unit where they were made. Every dynamic page item was editable. Published updates went Live immediately.
True/Slant Suggests
A lot of clever engineering, parsing, processing, and weighting of content, activity streams, and social signals fed True/Slant Suggests. We applied this same approach to B2C and B2B products and tools for writers, editors, marketers, sales folks. Choose writers, topics, and news sources to follow: Each selection focuses suggested Contributors: Suggestions were informed by whatever…
Reporting, Analytics & Insights
Engagement Activities https://meanbusiness.com/2019/10/29/data-reporting-insights/ Reports and additional Deliverables are the foundation for the next rounds of updates and iterations made with our assistance or your team handles themselves.
Colophon
Hat-Tips and Tools for Working
Recency, Frequency, and Time Spent
We pull recency, frequency, and time spent stats from historical application and tool usage early in the process. With SaaS and in-house business apps, people recognize tasks they worked on this morning and yesterday in this same app and that's helpful context. Mapping frequent tasks to existing shortcuts is quick Time To Return on Investment.…
Core Infrastructure Supporting People and Business
CRM, CMS, and Measurement technologies are fundamental for working at scale across teams, shifts, and time zones. Having this core infrastructure in place lets you focus on your differentiators and building experiences at the scale you want to operate. CRM CRM technologies are core to supporting your business. Your contacts are customers, clients, colleagues working…
Artist Community Marketplaces
Artist community marketplaces let us solicit and manage custom contributions at scale. Each artist gets a custom experience. Artist teams see what's relevant in one place. Brands, sponsors, and co-marketing partners see campaign-level activities, assets and reporting approved by artist teams. Fans get exclusive access and clear pathways to earn more rewards through their participation.…
DAM, That’d be Great
I'm working to catalogue files I have on current workstations, servers, and a bunch old drives. My primary goals are having searchable file names, types, and their media sources catalogued via scan of multiple filesystem types. A text file is a fine end result. There are plenty of Great-to-Haves beyond this, but getting core requirements…
Authy’s Doing 2FA Well
gAuthenticator had been my go-to 2FA app since it was introduced. I've had recurring problems with it and started using Authy a few months ago. Most of my issues and requirements from this earlier post are addressed well by Authy. https://meanbusiness.com/2019/07/14/indications-are-theres-no-way-to-backup-and-restore-gauthenciator-tokens/ Authy lets me use tokens it syncs across multiple devices. I've got tokens available…
Curating Photo Archives
Photo.app helped me curate and catalog GBs of photos from twenty+ years of archives. It sped up the family project I was working on, raised my expectations for how Enterprise photo asset management can work, and compelled me to reconsider ways to take advantage of organizing the rest of my work and personal archives. During…
Rules for Negotiating a Job Offer
All 15 Rules and the whole Harvard Business Review article are worth reading. In two recent discussions with others who had offers on the table, we were optimizing for the first five rules: Likeability telegraphing your Yes Consider the whole deal Don’t negotiate just to negotiate, and Avoid, ignore, or downplay ultimatums of any kind Being courteous and…
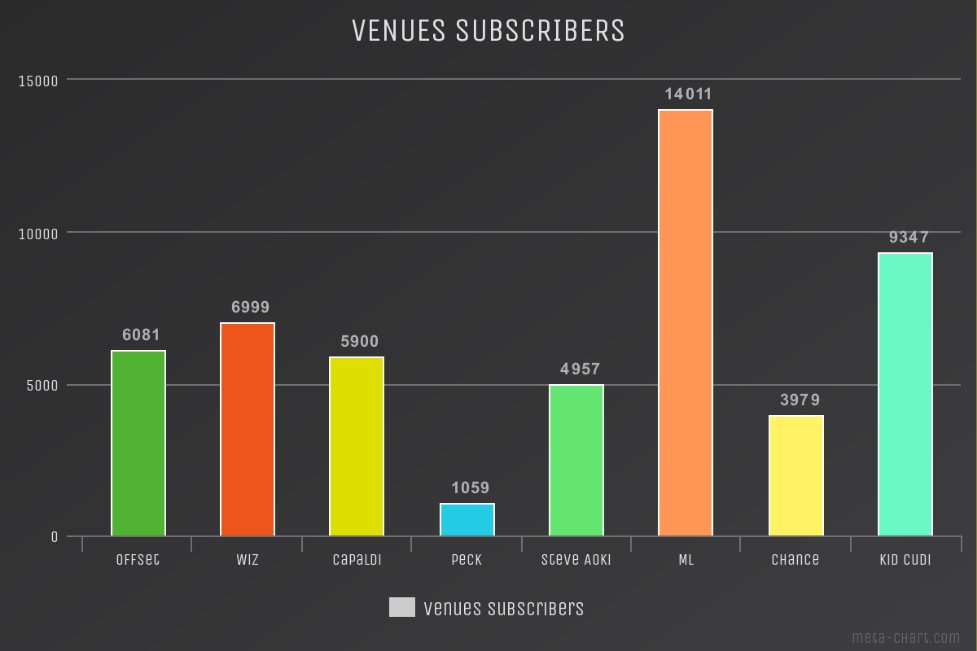
New Revenues and Sales Funnels
Revenue Generation @ Scale Standard ad slots surrounding Hearst Games were sold by internal teams and via auction to approved partners on private exchanges. Audience and Viewability details were available to all parties, and Hearst had access to significant 1st-Party demographic and psychographic info via detailed engagement metrics. Sponsorship and message integration for Beauty CPG…
Games @ Hearst
Games @ Hearst officially launched in partnership with Microsoft in 2016. Cosmopolitan, Esquire, and Good Housekeeping created games that were featured daily on msn.com and distributed across their own mobile, social and web properties. Tens of millions of people played and shared these games weekly. They showed us the topics they liked and the types…
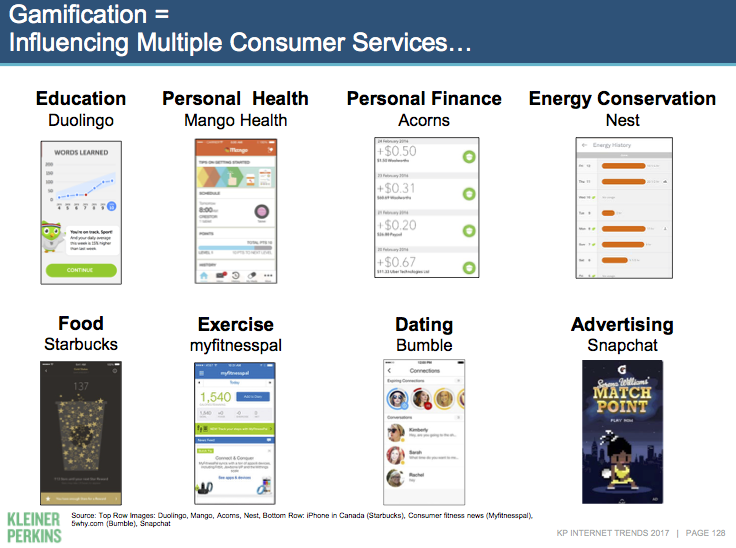
Games Optimize Learning & Engagement
Games are the Motherlode of Product Innovation / Evolution, & Modern Learning. Games are Foundational for Internet Services Games aren't just for some people -- 3.5 BILLION people regularly spend time laying games. Mary Meeker and Kleiner-Perkins spent 70 pages talking about Games in their 2017 Internet Trends report.
Optimize Learning & Engagement
Games are the Motherlode of Product Innovation / Evolution, & Modern Learning. Games are Foundational for Internet Services Games aren't just for some people -- 3.5 BILLION people regularly spend time laying games. Mary Meeker and Kleiner-Perkins spent 70 pages talking about Games in their 2017 Internet Trends report.